Proxmark3 Latest Version Replicator RFID Duplicator NFC Writer Proxmark 3 Access Control Card Reader USB Set Clone
As the factory updates the product, the appearance will be a little different and does not affect the performance. The pictures are for reference only.
The new machine shows v3, which is a printing problem. You can directly flash the v5 firmware without affecting the use. Please note
NOTE:The keychain in the product set has no remarks and is uniformly colored blue.
1. double port usb
2.From AT91SAM7S256 to AT91SAM7S512
Compared with the improvements of PM3 RD V2.0:
1. Built-in high-frequency antenna, matching antenna depth, eliminating blind spots, reading the entire data card without interruption.
2. Increase the frequency of the key, the size of the card can accommodate everything.
3. Data analysis, completely stable, and low error rate.
4. The low frequency antenna improves the signal-to-noise ratio, the recognition speed is higher, and the mobile design can meet various needs.
5. No antenna interface, no need to connect because it is easily damaged.
6. Cancel lithium battery, easy and convenient. (In offline mode, you can use mobile power)
7. Except that it has nothing to do with the original relay, it has low cost, light weight and easy to carry.
Compatible with all official firmware, can clean any version as needed.
Depending on your preference, you can use the official "command line" or "Proxmark Tool.exe" to work
(Low-frequency antenna is installed on the right)
Antenna #LF: 30.41 V @ 125.00 kHz
Antenna #LF: 22.01 V @ 134.00 kHz
#HF antenna: 28.43 V @ 13.56 MHz
(Low-frequency antenna is installed on the left)
Working voltage: 3.5-5.5V
Current work: 50-130mA
Length and width: 54mm * 86.6mm
Thickness: 6.2 mm (thinnest) 9.8 mm (with screws) 15.8 (with low frequency antenna)
Packing:
1. Proxmark3 (HF ANT with board) -------- 1 pc.
2. Replaceable UID card -------- 1
3. UID interchangeable keychain -------- 1 piece.
4. T5577 card -------- 1
Card operation mode:
1. Ordinary M1 S50 card reader and other Type B 14443A cards.
2. Analyze PRNG 0 using department-specific security.
3. Use embedded (mfoc) security to solve the entire map.
Analog card mode:
1. Simulate the user ID of Mifare S50 / Ultralight / DESFire series cards.
2. Analog data M1 S50 for the entire sector. (Select card reader)
3. Simulate the shell M1 S50 and obtain the data used to calculate the key (select card reader)
Silent mode:
1. A quiet data transmission analyzer between the M1 S50 card and the card reader, analyzing the key.
2. 14443A Class B silent card reader with full communication function.
The reader is used for debugging and analyzing actions.
Low frequency:
Card operation mode:
1. Read ID, HID, T55XX, Indala and other low frequency cards.
2. Use T55XX ID / HID / Indala recording card to turn it into three cards.
Analog card mode:
1. Enter the ID / HID card, which is an analog of the specified card type.
2. Analog modulation scheme, indicated data card and ASK / FSK / PSK
Silent mode:
1. Quietly sniff data between card and reader (less, untested)































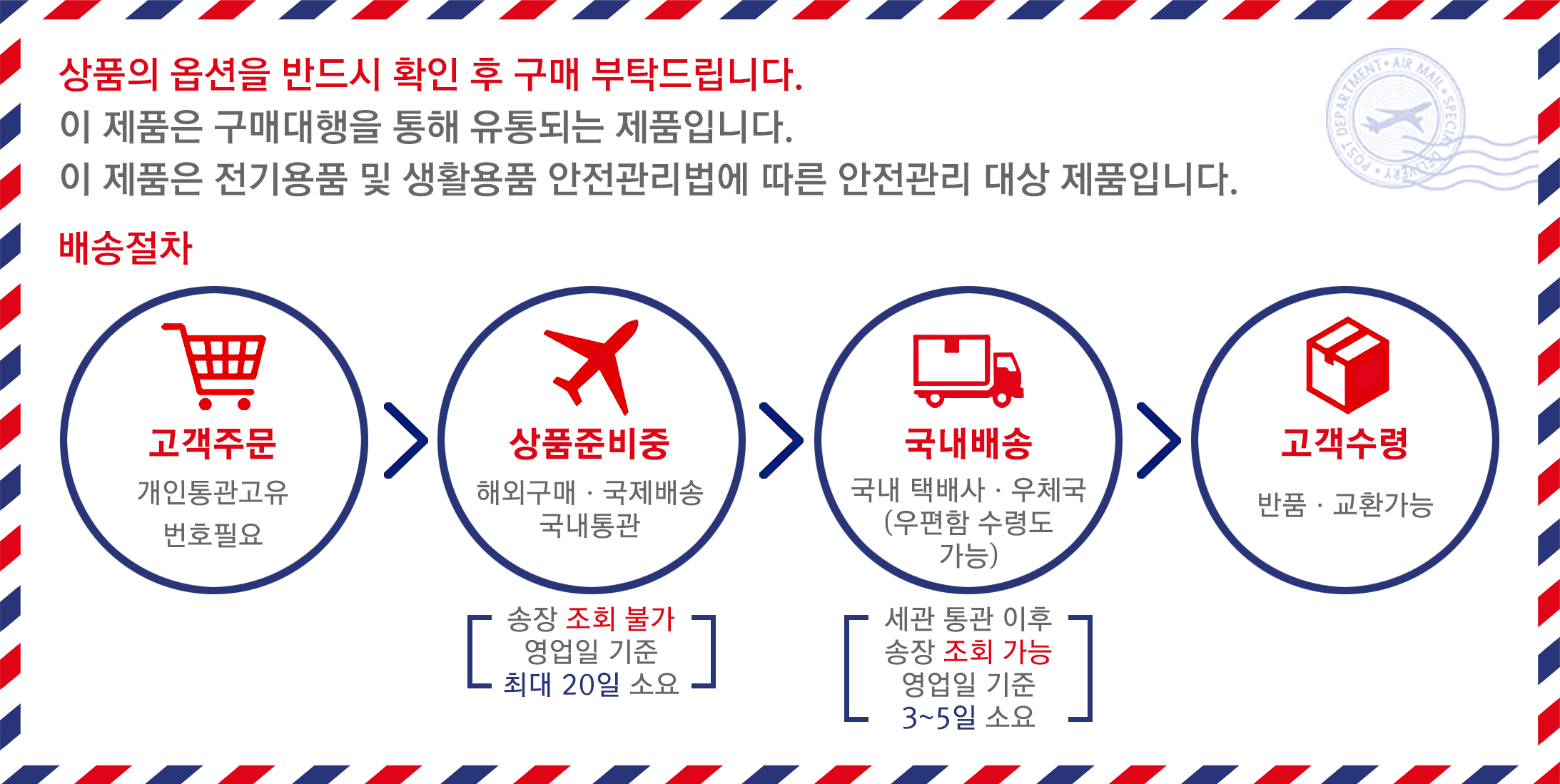
 배송기간
배송기간